The Ukrainian crisis shows has heightened awareness of risks to cloud infrastructure affected by political or natural disasters.
By Susan Bradley
Contributing Writer, CSO |
We live in an always-on world of 24/7 websites, servers, help desks and internet connectivity—that is, until it’s not connected. The Ukrainian crisis shows that IT and security admins of Microsoft environments need to be aware of geographic and other risks they might not have considered yet.
As we move servers to the cloud, have we considered the impact of geographic and geopolitical issues and boundaries? Cases in point:
Any international business must think about local security and privacy policies and regulations they must follow to be compliant everywhere they operate. If you do business in Germany, you must abide by the European Union’s General Data Protection Regulation (GDPR), which governs how personal data of individuals in the EU may be processed and transferred. Have customers in California? You are subject to security and privacy laws of both the United States and California.
Compliance with local data protection rules can be overwhelming. Layer on what is going on in Russia and overseas. Imagine if you or a critical third-party provider relies on a cloud service that is suddenly shut down or impacted by a geographic disruption. The disruption doesn’t have to be from a military or political crisis. I live in an area of the United States that is under a constant threat of an earthquake. How can you limit all these risks?
Know where your data goes
Knowing the areas of the world your data travels through. Only by understanding where these geographic risks are can you plan ahead. Always plan on alternative locations to house the data. Ensure that your cloud deployments have redundancy or the ability to move to different data centers quickly and easily.
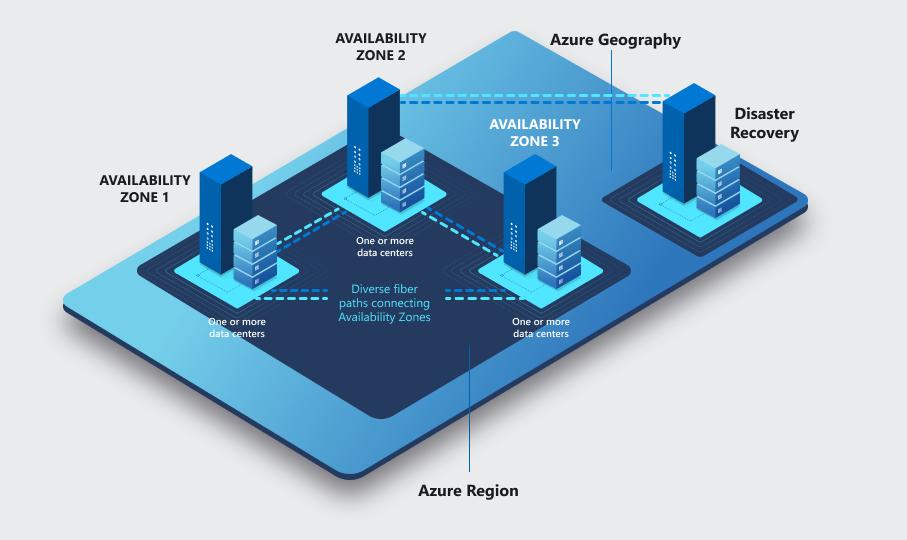
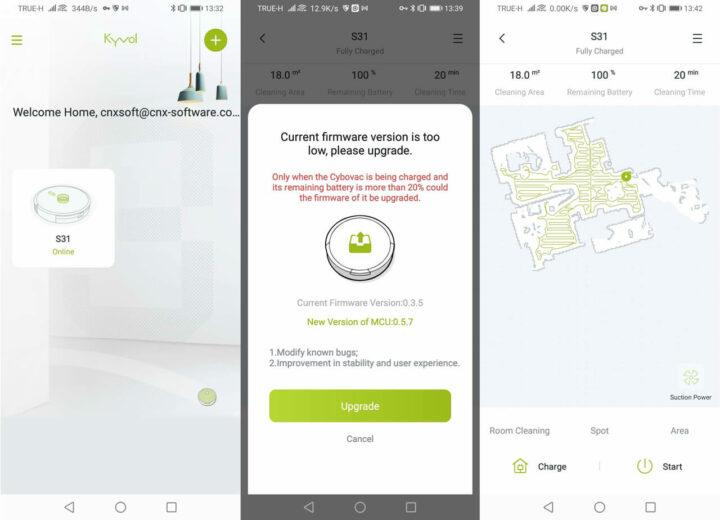
Consider using geo-zone-redundant storage (GZRS). As Microsoft notes, “Data is replicated synchronously across three Azure availability zones in the primary region using zone-redundant storage (ZRS), then replicated asynchronously to the secondary region. For read access to data in the secondary region, enable read-access geo-zone-redundant storage (RA-GZRS). Microsoft recommends using GZRS/RA-GZRS for scenarios that require maximum availability and durability.”
Work with compliance teams to meet local privacy and security requirements
Compliance and privacy, while necessarily security related, are often intertwined. Cloud security teams need to work with compliance teams to ensure that solution deployments meet a country’s requirements.
SharePoint and Teams is often the first online platforms that push your firm to start considering compliance needs. Start by planning your multi-factor authentication (MFA) needs and requirements on that platform. Whether you look to native Microsoft or third-parties, your best bet to control access is to roll out MFA.
Next, review external access in Teams. It enables external access by default, which means your organization will allow Teams messages from those outside of your domain. Attackers have also infiltrated Teams with bad actors sending Trojan-loaded documents and files on Teams via the chat section. Consider carefully your Teams access policies depending on your risks and business needs.
You can set conditional access policies that allow access to Microsoft cloud assets based on user location and IP addresses. SharePoint and OneDrive can limit access. You can also limit access to unmanaged devices so that only firm-approved technology assets can obtain access to your resources. Always review what security and compliance tools are being added to SharePoint, OneDrive and Teams. Limit user access to only the data they need.
Make sure you have the proper Microsoft licenses
You may need additional licenses to implement these conditional access policies. Many of Microsoft’s security and compliance offerings require additional licensing. For example, you need a license ranging from Office 365 E5/A5/G5, Microsoft 365 E5/A5/G5, Microsoft 365 E5/A5/G5/F5 Compliance, Microsoft 365 F5 Security & Compliance, or Microsoft 365 E5/A5/G5 eDiscovery and Audit to enable Advanced Audit in Microsoft 365. Advanced Audit provides one-year retention of audit logs for user and admin activities and provides the ability to create custom audit log retention policies. Many countries require you to maintain access logs.
Conditional access, one of the most powerful tools to ensure compliance with geographic needs, requires Azure Active Directory Identity Protection, which is tied to an Azure P2 license. Conditional access can be rolled out to specific groups of users that need the additional protection. Scope the use of conditional access by assigning risk policies to allow access for licensed users only. You may need to have different licenses for users located in a geographic region to better protect them and comply with local regulations.
You can always go back and add users to the data sharing, but it’s extremely hard to undo a link that was shared widely. That could end up not only in inboxes, but in cloud backups, persona devices and other platforms that you can’t easily pull it back from.
Run simulations to better prepare for disruption
Use the Ukrainian situation to run “what if” analyses even if you aren’t impacted today. What if a datacenter in Texas was impacted by a power issue or natural disaster? What if a server overseas was impacted by a local issue? What if a cloud server cannot continue to operate? Can you pivot and move quickly to alternatives? Do you know right now where your servers are located? You need to ensure that you can answer these questions so you can then provide alternative plans for your organization.
We once used to be concerned about the risk of on premises servers and the reliance on one physical location. We need to do similarly for cloud services. Know the geographic risks and limit that risk accordingly.
Related:Copyright © 2022 IDG Communications, Inc.
22 cybersecurity myths organizations need to stop believing in 2022Copyright © 2022 IDG Communications, Inc.